Posted inNews
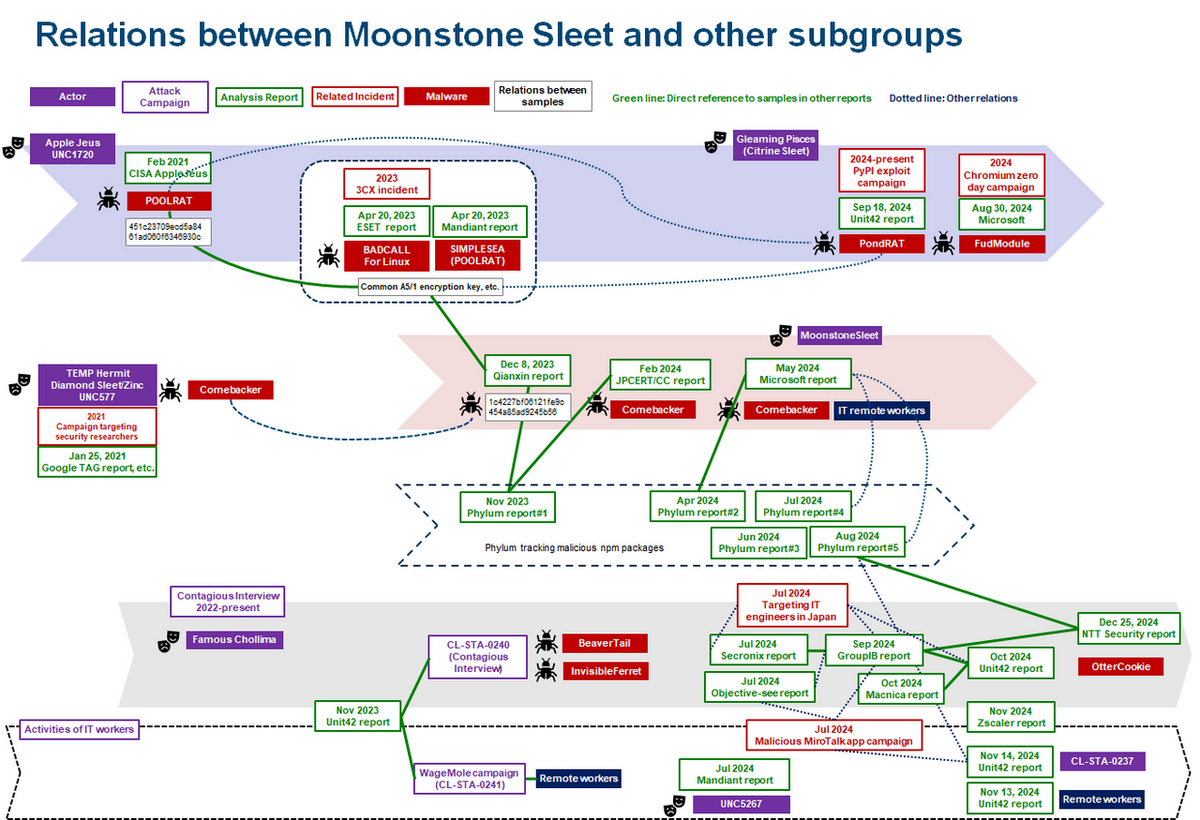
From Cyber Security News – Lazarus Group is No Longer Consider a Single APT Group, But Collection of Many Sub Groups
The cybersecurity landscape is witnessing a growing complexity in the attribution of Advanced Persistent Threat (APT) actors, particularly the North Korean-linked Lazarus group. Once considered a singular entity, Lazarus has…

.webp)
.webp)